HEIR Platform
In the landscape of healthcare, significant challenges emerge in the realm of cybersecurity. The healthcare sector is increasingly becoming a prime target for cyber-attacks, necessitating heightened defensive measures. Unfortunately, there is a notable absence of comprehensive risk assessment mechanisms tailored to the healthcare domain, leaving critical vulnerabilities unaddressed. An additional concern arises from the limited availability of effective anomaly detection mechanisms, leaving healthcare systems prone to undetected breaches. Trustworthiness of healthcare-related data remains a hurdle, as robust mechanisms to ensure data integrity and authenticity are lacking. Furthermore, the scarcity of benchmarks for comparable healthcare organizations hinders the establishment of best practices and standards. Lastly, a noteworthy gap exists in the form of an intelligent knowledge base accessible to diverse stakeholders, inhibiting collaborative efforts to combat evolving threats effectively.
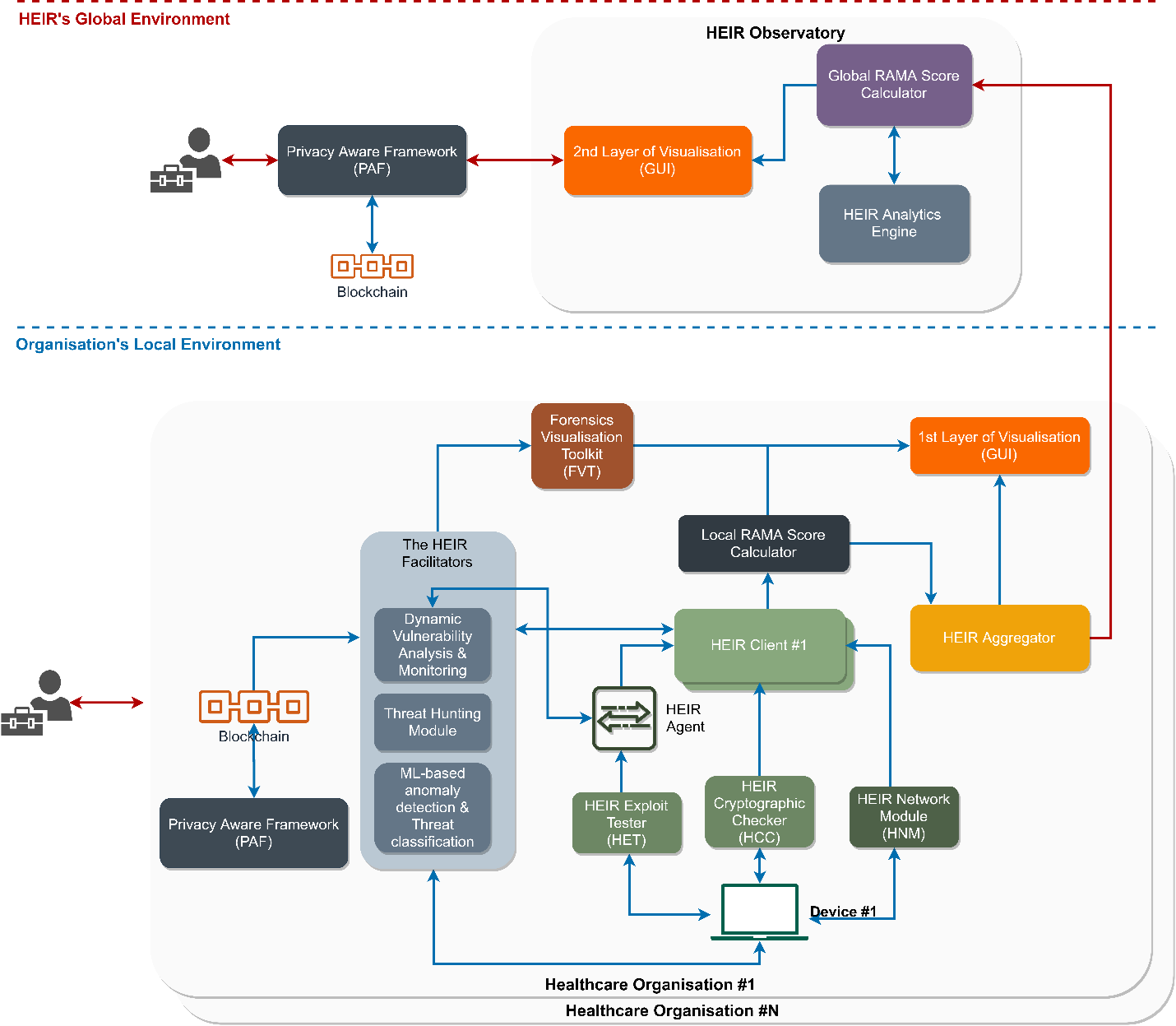
A framework that provides real-time threat-hunting capabilities, facilitated by advanced machine learning technologies, leads to the creation of the Risk Assessment for Medical Applications (RAMA) score in a local and global environment. Moreover, HEIR offers the Privacy-Aware Framework that enables sensitive data trustworthiness sharing by leveraging blockchain capabilities. Lastly, HEIR offers an intelligent knowledge base accessible to different stakeholders, providing advanced visualisations for each threat identified in RAMA and facilitating global awareness of EMD-related threats.
A holistic cyber-intelligence platform for a secure healthcare environment that provides real-time threat-hunting capabilities, facilitated by advanced machine learning technologies, leads to the creation of the Risk Assessment for Medical Applications (RAMA) score in a local and global environment. Moreover, HEIR offers the Privacy-Aware Framework that enables sensitive data trustworthiness sharing by leveraging blockchain capabilities. Lastly, HEIR offers an intelligent knowledge base accessible to different stakeholders, providing advanced visualisations for each threat identified in RAMA and facilitating global awareness of EMD-related threats.
Security And Privacy Assurance Suite
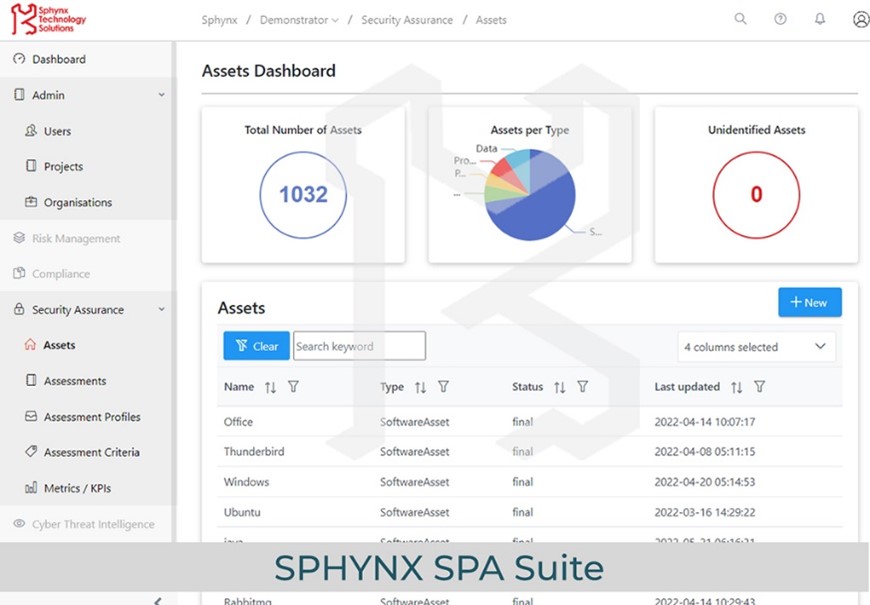
In the realm of organizational security, several crucial endeavours emerge. The first involves certifying the security attributes of services, ensuring they adhere to established standards for safeguarding user data and interactions. Simultaneously, security assessments and certifications for industrial sites are imperative, scrutinizing physical and digital safeguards to fortify critical infrastructure. Evaluating and certifying processes constitute another facet, embedding security measures into operational workflows to mitigate vulnerabilities. Additionally, the pursuit of economical solutions for security audits remains vital, allowing comprehensive evaluations of security systems, policies, and practices without excessive financial burdens.
A suite supporting hybrid security and privacy assessments that include and combine a) Automated threat analysis and vulnerability analysis, b) Static analysis, c) Penetration testing, and d) Continuous runtime monitoring.
Shared situational awareness, preparedness and coordinated incident response in alignment with the NIS Directive-established EU cybersecurity structures and mechanisms.
Observatory
Cybersecurity incidents have shown that the healthcare sector is one of the most vulnerable to cyberattacks. National Cyber Security Authorities, regulators, policymakers and insurance companies lack a benchmarking methodology and relevant KPIs for assessing the cyber-security status of organisations belonging to a particular domain, especially health. At the same time, there is no unified platform to observe the security status of electronic devices and provide real-time forensics in healthcare environments, such as a group of hospitals and medical centres.
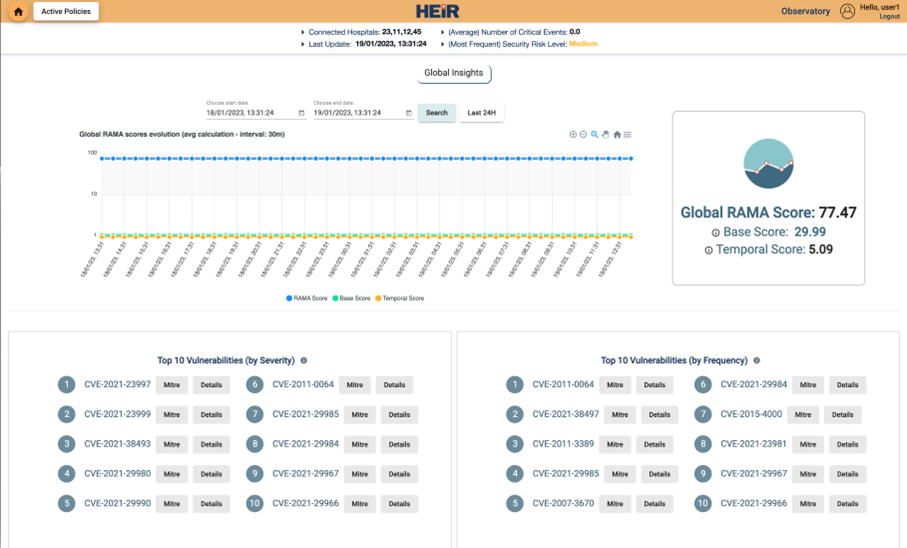
A cybersecurity solution that offers automated and up-to-date information on how a particular organisation stacks up against other entities belonging to the same domain along with tools for effectively monitoring and understanding a hospital’s cybersecurity status in real-time.
The Observatory, in a large scale of connected hospitals, serves as a key means of measurement of cybersecurity status among healthcare organizations. The Risk Assessment for Medical Applications (RAMA) provides a score and metadata that could help the assessed healthcare organization realize its security posture. The Global RAMA Score is a weighted sum of the Local RAMA aggregated scores of the HEIR-connected hospitals. As a result, the Global RAMA Score may be compared to the Local Rama Score of the connected hospitals, thus understanding the hospital’s cybersecurity status in real-time. Furthermore, the Active Policies of the Observatory can be used as a knowledge base for policy makers. There is no alternative solution to this issue, thus Observatory as a service is innovative. Finally, the cybersecurity status of hospitals may be used by insurance companies to offer more attractive contracts and handle cybersecurity claims.
HEIR SIEM
As technology advances, there is a growing need for effective and efficient tools to deal with the increasing number and frequency of cyber-attacks. Specifically, the increasing sophistication of cyber-attacks led organizations to increasingly seek comprehensive threat detection and response capabilities to counter these sophisticated attacks effectively. Organizations across various sectors, including finance, healthcare, and e-commerce, recognize the importance of proactive threat detection and prevention. The market is highly competitive, with several established players and emerging startups offering real-time threat-monitoring solutions.
Provide a system that helps organizations proactively monitor, detect, respond to, and investigate cybersecurity threats and incidents, all while maintaining compliance with industry regulations.
HEIR’s SIEM offers a compelling value proposition by enhancing security posture, enabling proactive incident response, providing situational awareness, optimizing resource utilization, ensuring compliance, and leveraging continuous threat intelligence. By adopting such tools, organizations can fortify their defences and stay ahead of the constantly evolving threat landscape. Unlike other solutions available in the market, the SIEM stands out with its fully customizable nature and comprehensive set of state-of-the-art technologies delivered by a team of security experts. Its flexibility and robustness empower organizations to strengthen their security posture by monitoring several parameters such as devices’ system events, Load and Memory Usage, Drive space, etc. With an intuitive, centralized monitoring interface, it offers numerous pre-built integrations, including renowned antivirus (e.g., BitDefender) and firewall (e.g., Symantec DLP, FortiGate firewall) solutions, as well as the ability to integrate with a growing list of market-leading software solutions.
Forensics Visualisation Toolkit (FVT)
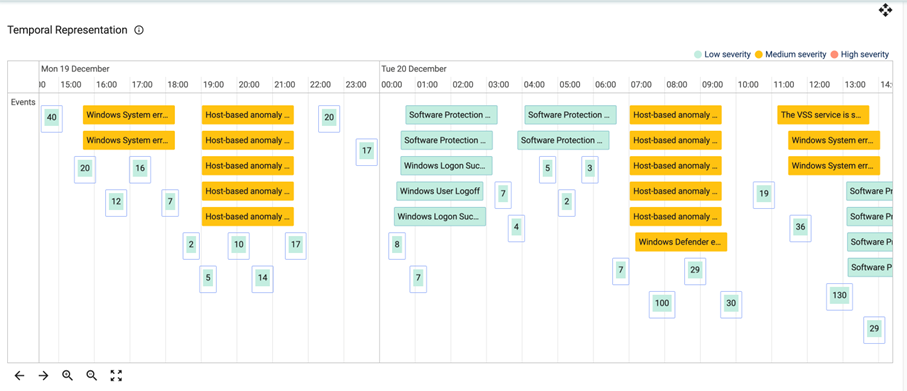
Difficult exploration from big volumes of multidimensional data could lead to slow reactions in cases of security breaches as well as not discovering potential threats.
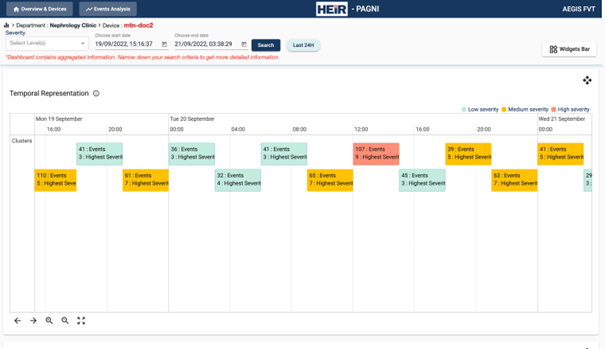
Digital forensics analysis, also known as computer forensics or cyber forensics, focuses on investigating and analyzing digital devices and electronic evidence to uncover information related to cybercrimes, data breaches, and other digital incidents. It involves the identification, preservation, extraction, and interpretation of data from various digital sources. Digital forensics analysts utilize specialized tools, such as the Forensics Visualization Toolkit (FVT), and techniques to examine digital devices such as computers and network systems.
FVT offers a solution that can handle large number of heterogeneous events and provide intuitive visualisations for IT and non-IT experts that reveal hidden relationships and insights.
Local and Global RAMA
Although the healthcare sector has been capitalizing on digital advancements to improve patient outcomes and experiences substantially, poor security practices are still heavily used. Poor computer and user account security, remote access and home working, and lack of encryption are critical issues in the healthcare sector. These, in combination with the lack of up-to-date risk assessment techniques and security awareness, have led the healthcare sector to be one of the most impacted in terms of average data breach cost, as well as be the sector that faces the most significant influx of cyber-attacks, regarding both volume (69%) and complexity (67%).
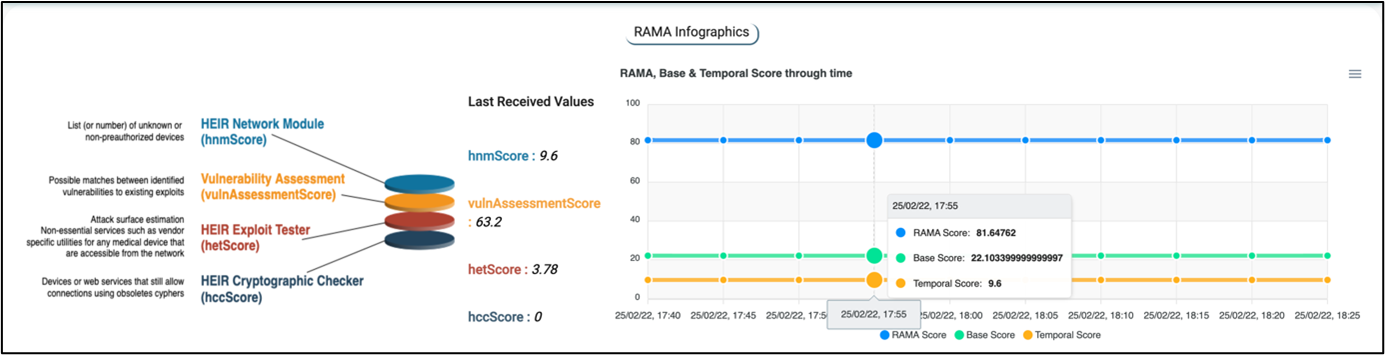
HEIR advances the state-of-the-art by proposing a novel Risk Assessment for Medical Applications (RAMA) score, which acts as a benchmark and estimates medical devices' attack surface and resilience by incorporating several critical issues. The Local and Global RAMA Score incorporates several critical issues reported by a centralized client and estimates the attack surface and the resilience of the underlying medical devices per healthcare organization.
The Local and Global RAMA score are innovative risk assessment metrics that were defined and developed within HEIR. The proposed solutions were based on existing state-of-the-art solutions, such as the CVSS, and are tailored -but not explicit- for the healthcare sector.
Privacy-Aware Framework
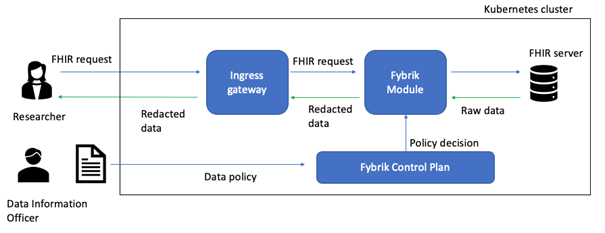
Access to sensitive medical data needs to be strictly controlled in order to be compliant with regulatory laws. Data access policies may change over time, and therefore should not be hardcoded into application logic. Additionally, traditional role-based access control (RBAC) systems do not give fine-grained access to such attributes within healthcare models.
Creation of a flexible and powerful framework to enforce policy-driven data compliance.
The Privacy-Aware Framework uses Open-Source code to allow for a highly flexible and powerful framework to enforce policy-driven data compliance. Access to data from medical data stores is fine-grained and does not require any modifications to backend storage systems.
Blockchain-based auditing mechanism
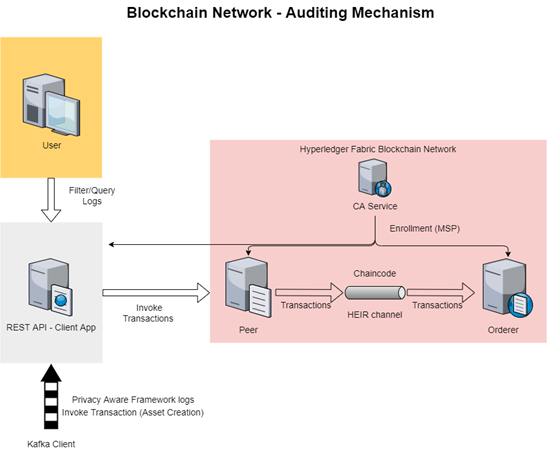
Auditing mechanisms play a crucial role in addressing the problem of trust, transparency, and accountability in various domains. Traditional auditing processes often suffer from inefficiencies, lack of transparency, and the potential for manipulation or fraud.
Provide an immutable record of all data access attempts, a filtering mechanism to identify malicious unauthorized access attempts on a regular (daily, weekly, monthly etc.) basis, and a timeline of events in the form of abnormal data access requests, facilitating the trace of malicious user behaviours back in time.
The unique selling proposition of the suggested blockchain-based solution that tackles this challenge, is built on the following advantages: (1) immutability and transparency; (2) decentralization; (3) enhanced data integrity; (4) real-time auditing and continuous monitoring; (5) smart contracts support and corresponding automation; (6) enhanced privacy and confidentiality and (7) cost-efficiency.
HEIR Client
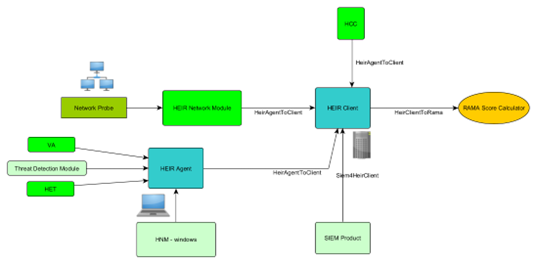
The use of un-synced services and solutions comes without the adaptability required by very different healthcare landscapes i.e., each European country has its own regulatory policies, and each healthcare unit has its own hardware and software infrastructure forcing the professionals to navigate a very complex landscape to obtain minimum cybersecurity.
A client that will allow for the collection of events from multiple sources that will be able to aggregate and correlate them.
The HEIR Client offers (i) Unified security and analytics for various environments with easy administration; (ii) Advanced threat intelligence built-in based on collaborating with project pilots and academia; (iii) Better return on investment determined by engineering the complexity out of security, to reduce risk at a lower total cost.
ML-based Anomaly Detection
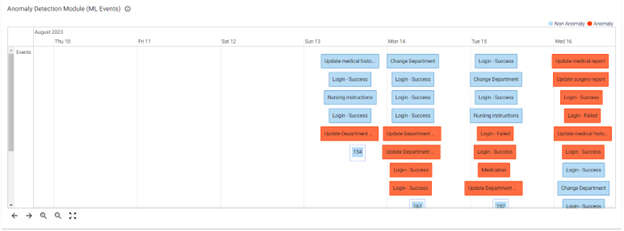
As healthcare organizations continue to embrace digital transformation and data-driven decision-making, the importance of robust anomaly detection solutions will only grow, marking a significant step towards ensuring a safe and secure healthcare ecosystem in the face of evolving cyber threats. With anomaly detection playing a pivotal role in safeguarding sensitive information and ensuring uninterrupted operations, the HEIR platform delivers comprehensive and tailored cybersecurity solutions to safeguard health systems and essential services in an increasingly digitized world.
Combining specific rules and novel ML models, the Anomaly Detection module intelligently classifies threat data, enabling health systems to respond proactively to potential security breaches. The module's versatility is exemplified by its capability to tailor the selected ML model or algorithm to the specific use case, whether supervised or unsupervised learning.
The adaptability and scalability of the Anomaly Detection module within the HEIR platform empower health systems with tangible and visually represented results via the FVT toolkit. The module's ability to effectively identify and prioritize cyber threats enhances the overall cyber security posture, making the HEIR platform a transformative solution for the healthcare industry.
